Detect Active Compromise on Your Network Edge
Gain visibility into compromised devices by analyzing inbound scanning activity and outbound communication with attacker-controlled infrastructure
Overview
Threat actors target edge devices like firewalls, VPNs, and routers to build botnets, stage malware, and maintain command-and-control. Once compromised, these devices either scan for new targets or quietly call back to attacker infrastructure. Today's threat actors use botnets to scan for vulnerable systems and launch mass, automated attacks. To do this, compromising edge systems are critical to their operations.
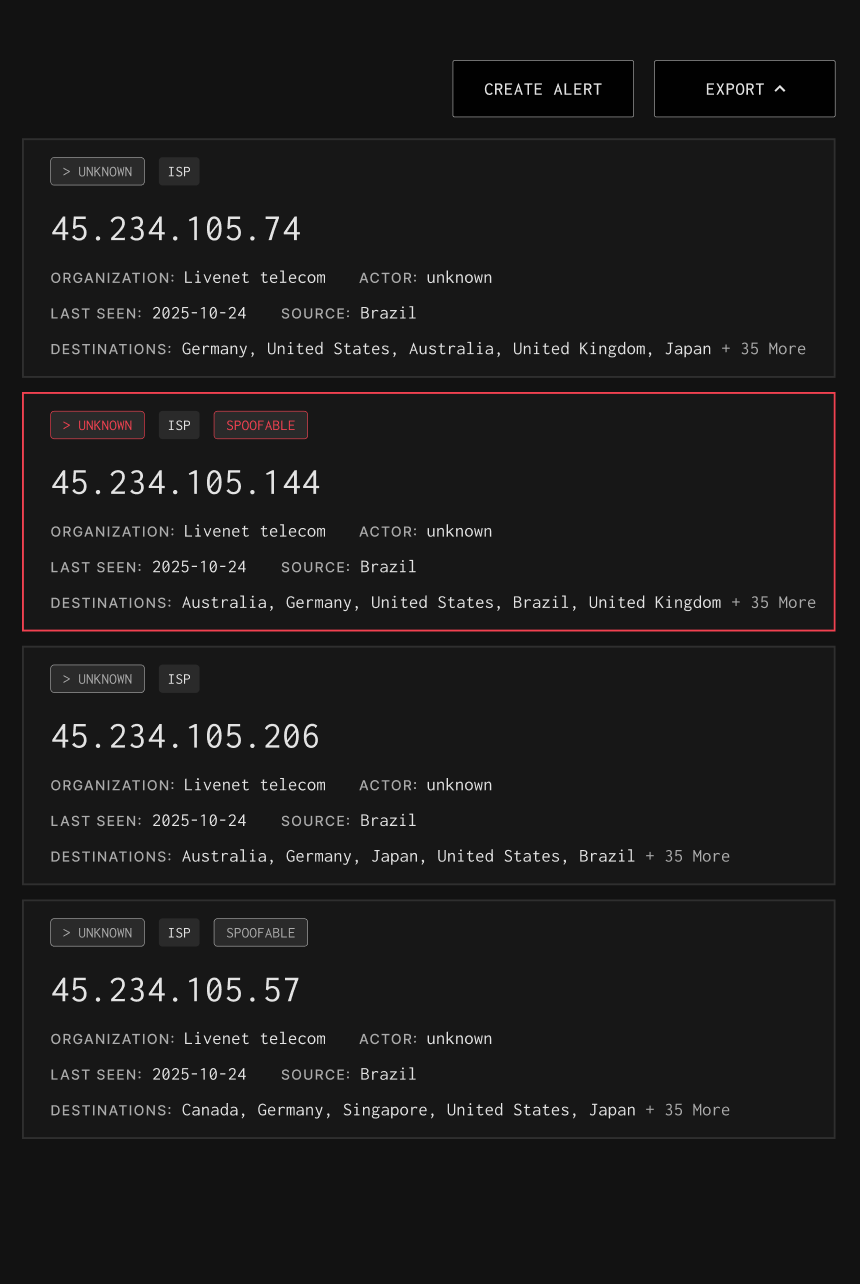
GreyNoise helps you spot compromised edge hosts fast using two independent signals. If your IP shows up as a scanner in GreyNoise, it’s likely been pulled into a botnet. If your outbound traffic matches a confirmed callback IP, it’s calling home to an attacker. Both are high-confidence indicators of compromise, even where EDR doesn’t exist. Compromised devices often behave like attacker infrastructure, making it likely that a compromised device will probe the GreyNoise sensor network or interact with a known malicious IP.
How GreyNoise Helps You
Find Your Compromised Assets
Identify Abnormal Outbound Traffic
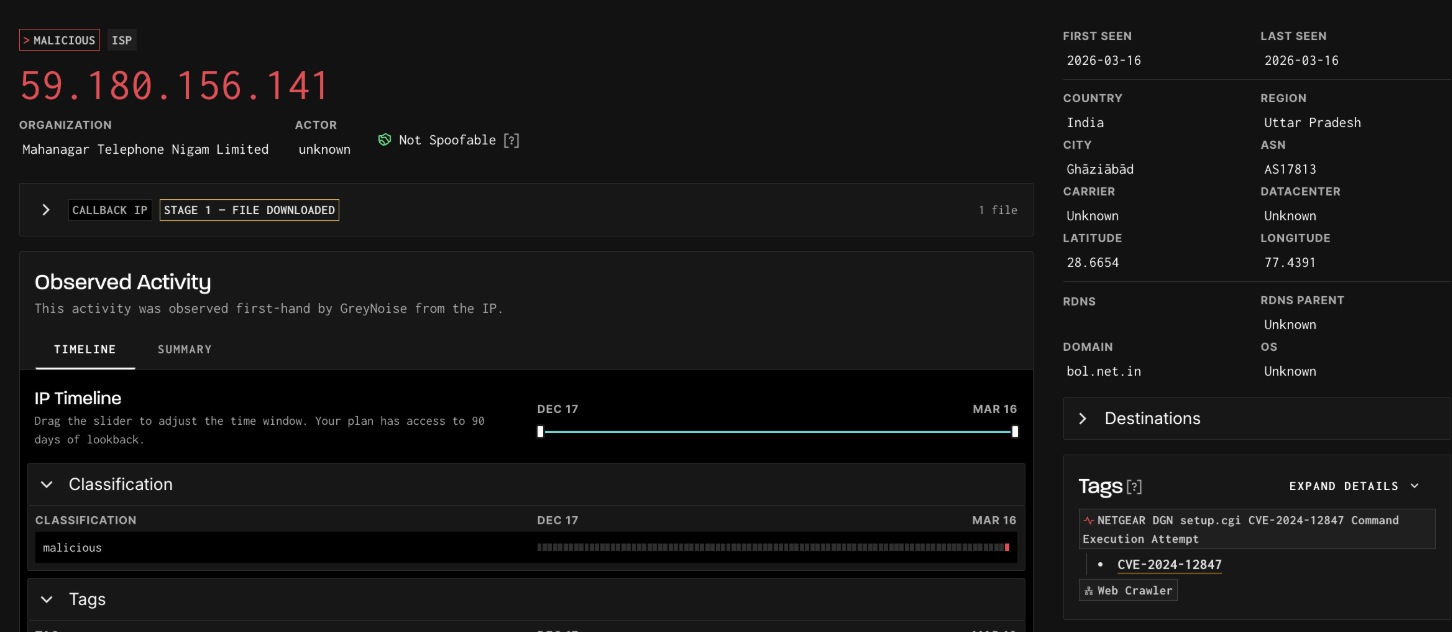
GreyNoise matches your outbound traffic against confirmed malicious and callback infrastructure derived from real exploit activity. A hit is a high-confidence signal that a device is calling out to attacker-controlled systems.
Faster Containment
Early visibility into compromised assets, from both scanning behavior and outbound callbacks helps teams isolate hosts and respond before damage spreads.
Strengthen Incident Investigations
Combine scanner IPs, callback infrastructure, and malware hashes to investigate suspicious activity across both inbound and outbound signals.
Block Malicious Outbound Connections
GreyNoise provides query-based, dynamic blocklists that prevent devices on your network from communicating with both known malicious scanner IPs and confirmed C2 infrastructure.