Join the Collective.
Defend the Edge.
Deploy deception sensors, contribute device profiles, and write detection rules to strengthen global threat intelligence for everyone.
Everything Your Sensors Capture Is Yours to Work With
When you deploy a sensor through Project Swarm, every session is recorded with full fidelity. You see exactly what hit your sensor, what it sent, and how it behaved.
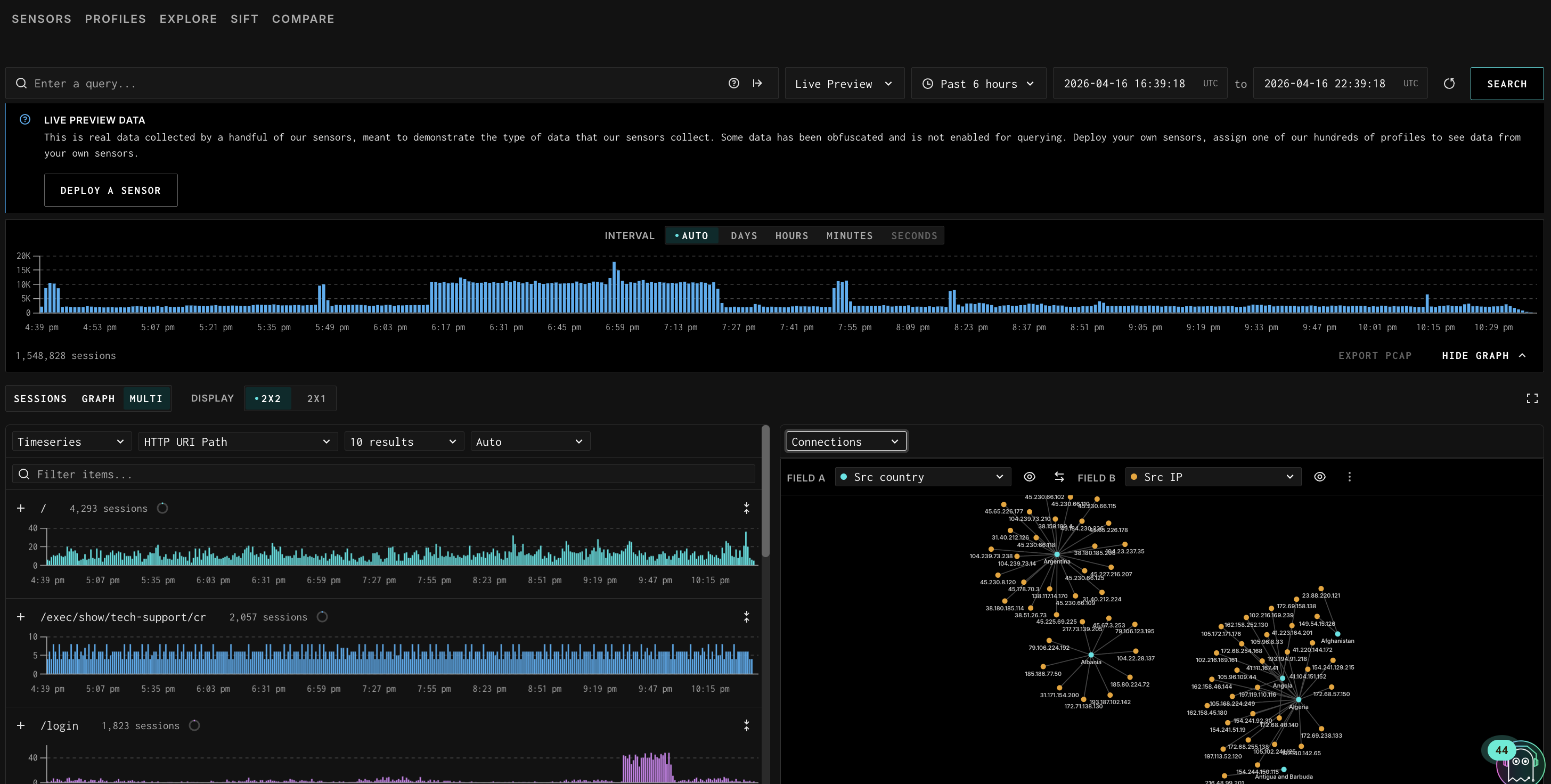
- View all traffic hitting your sensors via GreyNoise Explorer
- Compare your traffic against the global baseline to see what's uniquely targeting you
- Analyze raw PCAPs, payloads, HTTP headers, TLS metadata, and behavioral artifacts
- Write detection rules based on what you observe
- Use everything you collect for your own independent research
Deploy in minutes. Start contributing immediately.
1.
Register
Click the button below to get started. Sign in or create a Vizualizer account, then request access.
No subscription. No contract. This is a research initiative—and you’re in.
2.
Collect Real Attack Traffic
Deploy a lightweight sensor on your infrastructure to capture real attacker activity. See how adversaries probe, exploit, and interact with edge systems in the wild.
3.
Turn Insight into Protection
Analyze sessions, inspect payloads, and compare your traffic against the GreyNoise global baseline. Understand what’s targeting you and turn that insight into stronger protection for your team.




