GreyNoise observed 84,142 scanning sessions targeting SonicWall SonicOS infrastructure between February 22 and February 25, 2026. The activity originated from 4,305 unique IP addresses across 20 autonomous systems, with three operationally distinct infrastructure clusters executing coordinated VPN enumeration. Ninety-two percent of sessions probed a single API endpoint to determine whether SSL VPN is enabled — the prerequisite check before credential attacks. A commercial proxy service delivered 32% of campaign volume through 4,102 rotating exit IPs in two surgical bursts totaling 16 hours. CVE exploitation was negligible, confirming this as systematic attack surface mapping.
Why This Matters
SonicWall SSL VPN is one of the most documented initial access vectors for ransomware. Akira and Fog ransomware groups have repeatedly demonstrated that compromised SonicWall VPN credentials lead to full encryption in under four hours — with dwell times as short as 55 minutes. Five of seven SonicWall CVEs relevant to this attack surface appear in CISA's Known Exploited Vulnerabilities catalog, with four having documented ransomware use. The reconnaissance GreyNoise observed is the precursor phase — systematic target mapping that precedes exploitation.
Since March 2023, Akira alone has compromised at least 250 organizations and generated an estimated $244 million in ransomware proceeds, with 75% of SonicWall VPN intrusions attributed to Akira and 25% to Fog. More than 430,000 SonicWall firewalls are publicly exposed on the internet, with over 25,000 SSL VPN devices vulnerable to critical flaws and 20,000 running firmware that is no longer supported.
This is not the first time GreyNoise has observed this pattern. In December 2025, GreyNoise documented a coordinated credential campaign targeting both Palo Alto and SonicWall VPN infrastructure across 9 million sessions from more than 7,000 IPs, sharing identical client fingerprints across both vendors. The February 2026 campaign represents a continuation and intensification of VPN-focused reconnaissance.
Key Takeaways
- 84,142 sessions from 4,305 IPs in four days — Coordinated reconnaissance targeting SonicWall VPN enumeration and credential testing endpoints indicates systematic attack surface mapping
- 92% of sessions probed a single API endpoint — The VPN status check determines which devices have SSL VPN active, creating a target list for future credential attacks
- 32% of volume routed through a commercial proxy service — 4,102 exit IPs delivered 27,119 sessions in two surgical bursts, averaging 6.6 sessions per IP to evade rate-limiting
- Multi-vendor VPN reconnaissance — The Netherlands scanning cluster simultaneously targets SonicWall and Cisco ASA devices, indicating a broader VPN mapping operation
- Reconnaissance dominates — 92% of sessions targeted a single VPN status-check endpoint, confirming systematic target mapping rather than active exploitation
- Defenders should act now — Restrict management interface access, enforce MFA on SSL VPN, and patch CVE-2024-53704 (CVSS 9.8, CISA KEV) before reconnaissance converts to exploitation
What GreyNoise Observed
Campaign Timeline
The campaign exhibited four distinct bursts separated by a ∼31-hour low-activity period, with a persistent credential-testing baseline running continuously underneath.
Burst 1 — Initial Scan Wave (Feb 22, 00:00–19:00 UTC): The campaign opened with a 19-hour scanning wave peaking at 3,272 sessions per hour. This burst combined proxy infrastructure with the Netherlands scanning cluster, totaling 30,952 sessions on the first day.
Low-Activity Period (Feb 22 21:00 – Feb 24 04:00 UTC, ∼31 hours): Session volume dropped to a 54–90 session/hour baseline — exclusively the persistent NetExtender credential testing cluster operating on autopilot.
Burst 2 — Proxy Resurgence (Feb 24, 04:00–12:00 UTC): The proxy infrastructure reactivated for a focused 8-hour window, delivering 17,991 sessions through rotating exit IPs. Per-IP volume remained extremely low (average 6.6 sessions, maximum 13), consistent with a proxy service rotating exit nodes.
Burst 3 — Peak Hour (Feb 24, 15:00–17:00 UTC): 7,374 sessions in the 15:00 UTC hour — the single highest hourly count of the entire campaign — followed by 5,484 in the 16:00 hour. This burst originated from the Netherlands scanning cluster, not the proxy pool.
Burst 4 — Final Surge (Feb 25, 08:00–13:00 UTC): A final burst peaked at 5,899 sessions in the 11:00 UTC hour, indicating ongoing orchestration.

The dramatic February 23 lull — a 95% drop from the preceding day — is operationally significant. The scanning infrastructure did not fail; the persistent NetExtender cluster continued uninterrupted at its normal rate. The pause suggests deliberate operational scheduling.

What Is Being Targeted
Two SonicWall-specific paths dominate the campaign, accounting for over 99.5% of all sessions:
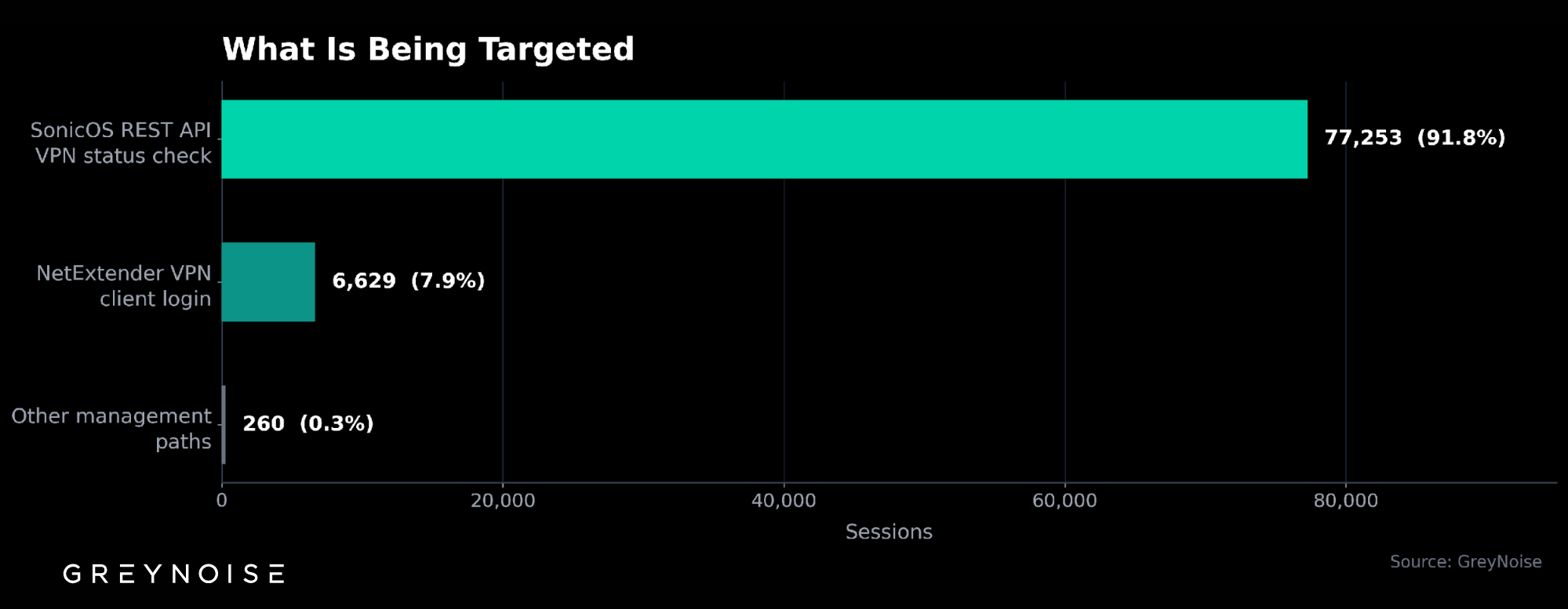
The overwhelming concentration on the VPN status API endpoint reveals the campaign’s objective: building a comprehensive list of SonicWall devices with active SSL VPN. This is a prerequisite for credential attacks — identifying which devices are worth targeting before deploying more expensive proxy resources for login testing.
Four Infrastructure Clusters
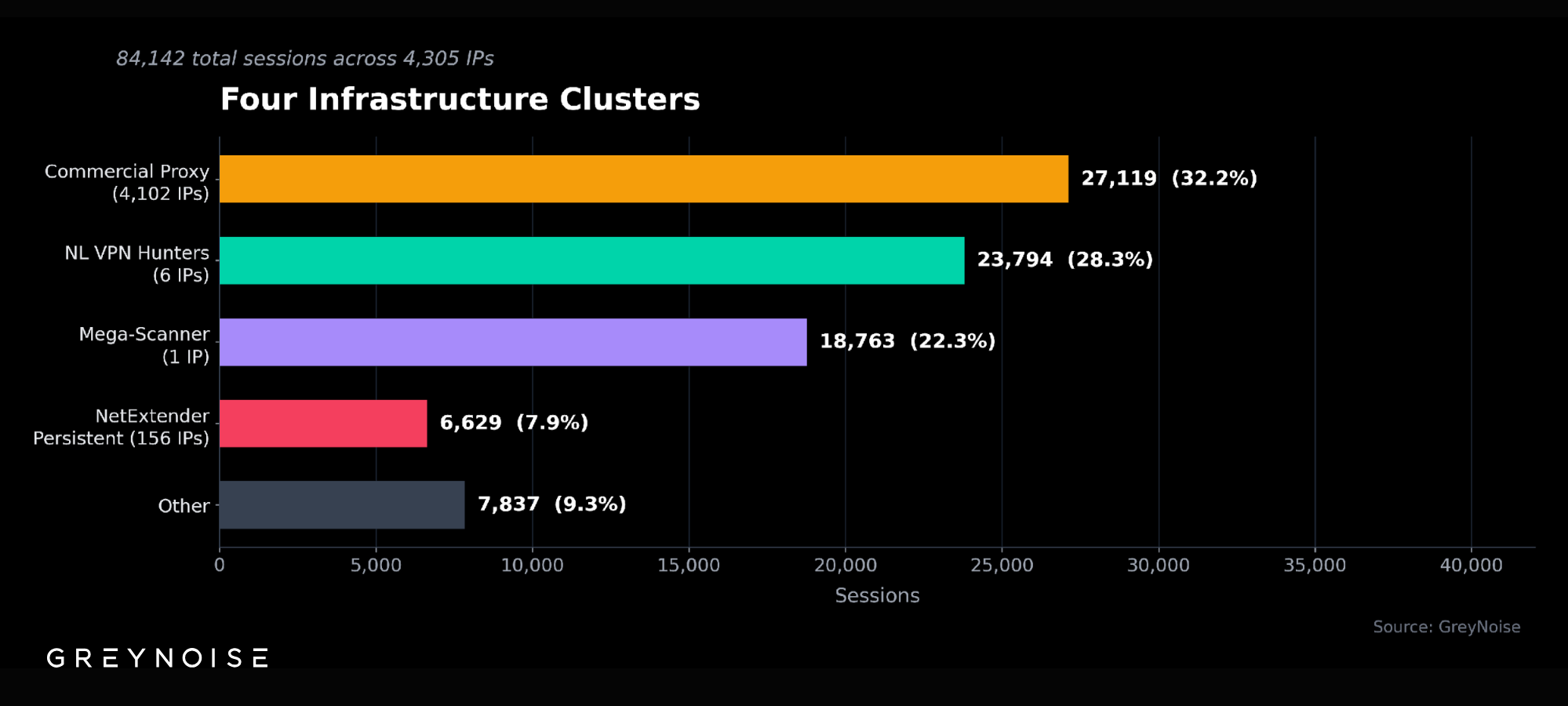
Cluster 1: Netherlands VPN Hunters (28% of Campaign)
Six IPs within a single Ukrainian-registered autonomous system (AS211736) operating from Amsterdam-based infrastructure delivered 23,794 sessions. These IPs run dual-vector scanning: VPN status enumeration paired with Cisco ASA reconnaissance, indicating a multi-vendor VPN mapping operation.
Censys infrastructure profiling revealed these nodes run identical software stacks. All share a single HASSH fingerprint, confirming deployment from a common provisioning template. Four of the six expose HTTP services on ports 7001–7003 with identical bare-minimum 404 responses — consistent with a custom scanning framework spawning worker threads.
Cluster 2: Commercial Proxy Spray (32% of Campaign)
27,119 sessions originated from 4,102 IP addresses in the 154[.]208[.]64[.]0/21 range, transiting through AS3257 (GTT Communications) from Canadian hosting infrastructure.
The proxy service — ByteZero (bytezero[.]io) — markets itself as offering 100+ million IPs across 150+ countries for web scraping and data collection. The scanning traffic originates from ByteZero’s paying customers, not the proxy infrastructure itself. ByteZero is the anonymization layer enabling the activity.
The proxy usage was surgical — concentrated in two primary windows:
A critical detail: ByteZero’s customer management platform went offline in early December 2025. The proxy nodes have continued operating for approximately three months without active abuse mitigation. This directly explains the unchecked scanning volume.
Cluster 3: The Mega-Scanner (22% of Campaign)
A single IP — 130[.]12[.]180[.]29 on AS202412 (Omegatech, registered in the Seychelles), geolocating to Germany — generated 18,763 sessions. This IP scanned across 20+ destination ports including non-standard ports (6666, 7777, 7443, 9443), cycling through 26 different browser user agents to evade basic fingerprinting.
Cluster 4: NetExtender Persistent (8% of Campaign)
156 IPs across four dedicated ranges maintain continuous credential testing at 54–72 sessions per hour against the NetExtender VPN login endpoint. This cluster uses a legitimate SonicWall VPN client identifier and never stops — it ran uninterrupted through the February 23 low-activity period. Total: 6,629 sessions over four days.
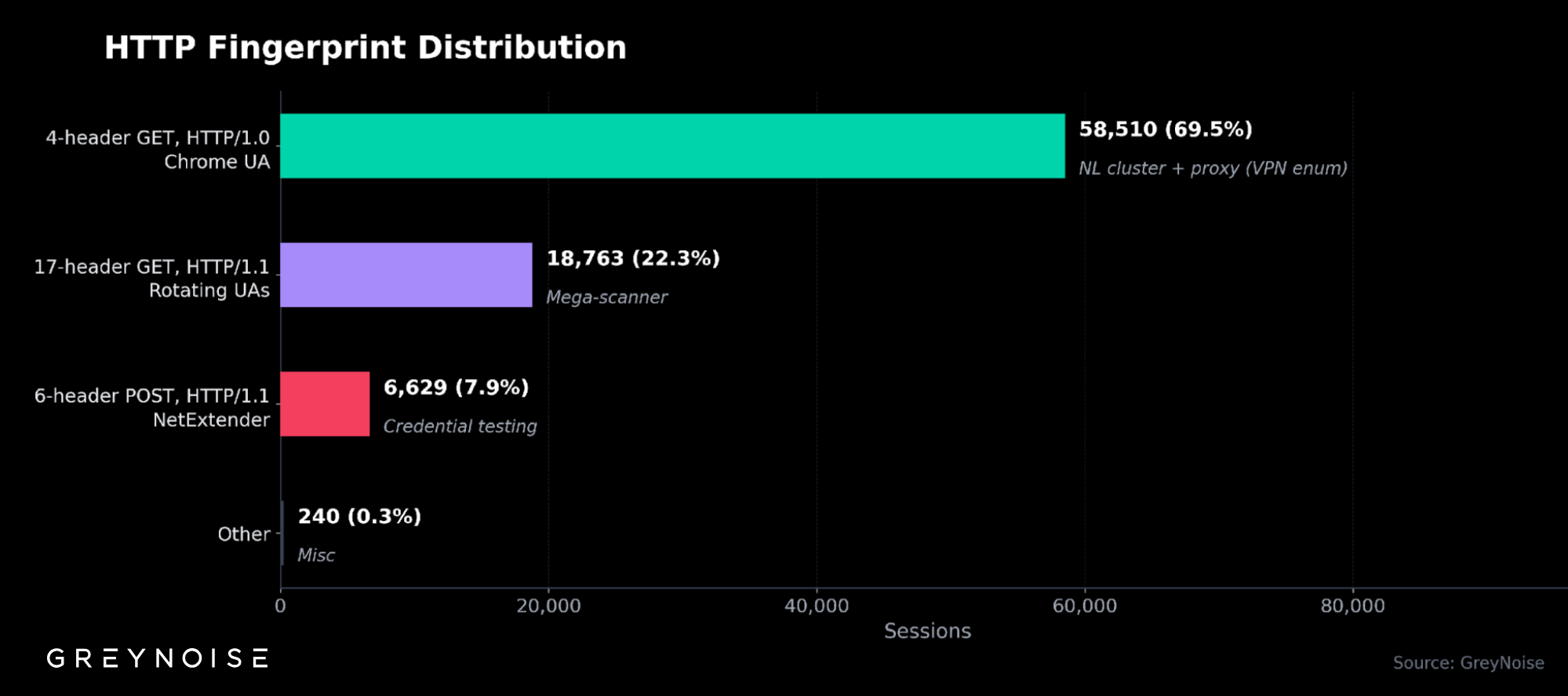
Fingerprint Analysis
A single HTTP fingerprint was present in 58,510 sessions — nearly 70% of the entire campaign. The associated user agent presents as a modern browser (Chrome 119 on Linux) but is paired with HTTP/1.0, a protocol version that legitimate Chrome browsers never use. This mismatch is a reliable, high-confidence indicator of automated scanning tooling.
Exploitation Assessment
Despite the reconnaissance volume, the campaign's behavioral profile is overwhelmingly pre-exploitation. 92% of sessions queried a single API endpoint to determine VPN status — a prerequisite check, not an exploit. GreyNoise maintains CVE-specific detection tags for six of the seven CVEs below; CVE-2024-40766 does not currently have a detection tag.
*CVE-2022-22274 and CVE-2023-0656 are detected by the same GreyNoise tag ("SonicOS RCE Attempt"). The 9 campaign sessions apply to both CVEs collectively.
.png)
Four of the five CISA KEV entries have documented ransomware use. The behavioral profile of this campaign — 92% concentrated on a single VPN status-check endpoint — is consistent with pre-exploitation reconnaissance rather than active exploitation. The targets identified during this mapping phase are likely to face exploitation attempts in the days and weeks ahead.
Strategic Implications
The use of commercial proxy services for VPN reconnaissance represents a maturation of the threat. Unlike botnets with fixed infrastructure, proxy services provide rotating datacenter IP addresses that are difficult to distinguish from legitimate traffic. The low per-IP session volume — averaging 6.6 sessions per exit node — is calibrated to evade rate-limiting and reputation-based blocking. Static blocklists cannot keep pace with infrastructure that rotates thousands of IPs within a single scan window.
The headless state of the proxy service — operating for three months without active abuse oversight after its management platform went offline — highlights a structural gap in the proxy ecosystem. When proxy providers lose the ability or incentive to police their customers’ traffic, their infrastructure becomes functionally equivalent to bullet-proof hosting.
This pattern is accelerating. In January 2026, Google disrupted IPIDEA — a residential proxy network used by over 550 threat groups including nation-state APTs — for credential stuffing and C2 obfuscation. The Shadowserver Foundation has tracked a separate campaign using 2.8 million IPs daily to brute-force VPN login portals. The proxy ecosystem has become the primary enabler of credential-based initial access.
Organizations running SonicWall firewalls should treat this reconnaissance as an early warning. The documented Akira ransomware kill chain begins with compromised SonicWall VPN credentials and achieves encryption in under four hours. SonicWall itself has confirmed that recent intrusions resulted from password reuse combined with CVE exploitation. The gap between the reconnaissance GreyNoise is observing and the exploitation that follows may be shorter than many organizations’ patching cycles.
Check If Your SonicWall Was Targeted (5 Minutes)
Step 1 — Check your logs (2 minutes). Search firewall logs for external requests to these paths between February 22–25:
- /api/sonicos/is-sslvpn-enabled (VPN status check)
- /sonicui/7/login/ (management interface)
- /cgi-bin/userLogin (VPN credential testing)
Step 2 — Check active VPN sessions (1 minute). Navigate to NETWORK | SSL VPN > Status in SonicOS 7.x. Look for sessions from IP addresses outside your user base, particularly from hosting or VPS providers.
Step 3 — Verify firmware and MFA (2 minutes). Confirm your SonicOS firmware is patched against CVE-2024-53704 (versions at or below 7.1.1-7058, 7.1.2-7019, or 8.0.0-8035 are vulnerable). Confirm MFA is enabled for all SSL VPN users.
If your SonicWall was probed and you are running end-of-life SRA appliances, disconnect them immediately — CVE-2021-20028 and CVE-2019-7481 have no patches available.
Recommendations
For Security Leadership:
- Audit SonicWall management interface exposure — administrative endpoints should never be internet-accessible
- Verify MFA is enforced on all SSL VPN users — credential stuffing is rendered ineffective by MFA
- Evaluate dynamic blocklists to address the IP rotation that makes static lists ineffective against proxy-based campaigns
- Treat VPN infrastructure as a priority patching tier — the reconnaissance-to-exploitation gap is narrowing
For Security Operations:
- Restrict access to /sonicui/7/login/ and /api/sonicos/ paths to trusted management IPs only
- Monitor for HTTP/1.0 requests paired with modern browser user agents — this combination is a high-confidence indicator of automated scanning
- Block identified scanning infrastructure at the perimeter:
- 154[.]208[.]64[.]0/21 (proxy exit nodes)
- 185[.]177[.]72[.]0/24 (bullet-proof hosting)
- 185[.]156[.]73[.]0/24 and 88[.]210[.]63[.]0/24 (scanner fleet)
- 204[.]76[.]203[.]0/24 (scanning with credential collection indicators)
For SonicWall Administrators:
- Patch SonicOS against CVE-2024-53704 (CVSS 9.8, CISA KEV) — SonicWall advisory SNWLID-2025-0003
- Reset all local user account passwords, especially those carried over during Gen 6 to Gen 7 migrations
- Decommission end-of-life SRA appliances — no patches are available for CVE-2021-20028 or CVE-2019-7481
- Enable login attempt lockout and password complexity enforcement (SonicOS 7.3+)
- SonicWall administrators running SonicOS 7.3.2 or NSM SaaS also have access to the Credential Auditor feature, which provides visibility into credential sprawl and reuse across the firewall environment
- Enable Geo-IP filtering and Botnet Protection on the firewall
View real-time GreyNoise data on SonicWall activity:
- SonicWall SonicOS API Scanner
- SonicWall SSL VPN Login Attempt
- SonicWall NetExtender Scanner
- CVE-2024-53704 Session Hijacking
- SonicOS RCE Attempt (CVE-2022-22274 / CVE-2023-0656)
- SonicWALL SRA SQL Injection Attempt (CVE-2021-20028)
- SonicWALL SRA SQL Injection Vuln Check (CVE-2021-20028)
- SonicWall SMA100 Arbitrary File Leak CVE-2024-38475 Attempt
- SonicWall SRA 4600 SQL Injection Attempt (CVE-2019-7481)