Ransomware attacks don't start with encryption. They start with reconnaissance—and we just watched a significant reconnaissance operation unfold over the Christmas holiday.
Between December 25–28, a single operator systematically scanned the internet for vulnerable systems, testing 240+ different exploits against targets and logging every hit. That data—a fresh inventory of confirmed vulnerabilities—will likely power targeted intrusions throughout 2026.
GreyNoise customers received this information early in our weekly At The Edge intelligence brief. For all IOCs and more detailed information, GreyNoise customers please check your inbox.
The Initial Access Broker model
Initial Access Brokers (IABs) are the advance scouts of the ransomware economy. They don't encrypt files or exfiltrate data. They build lists of exploitable systems and sell that access to operators who do.
Think of it as specialization. IABs focus on one thing: finding ways in. Ransomware crews focus on monetization. The handoff happens in criminal marketplaces where access to a vulnerable corporate network might sell for a few thousand dollars—or much more, depending on the target.
What we observed over Christmas was the supply-side of this market actively restocking inventory.
Campaign details
The operation ran from two IP addresses on CTG Server Limited (AS152194):
134.122.136.119134.122.136.96
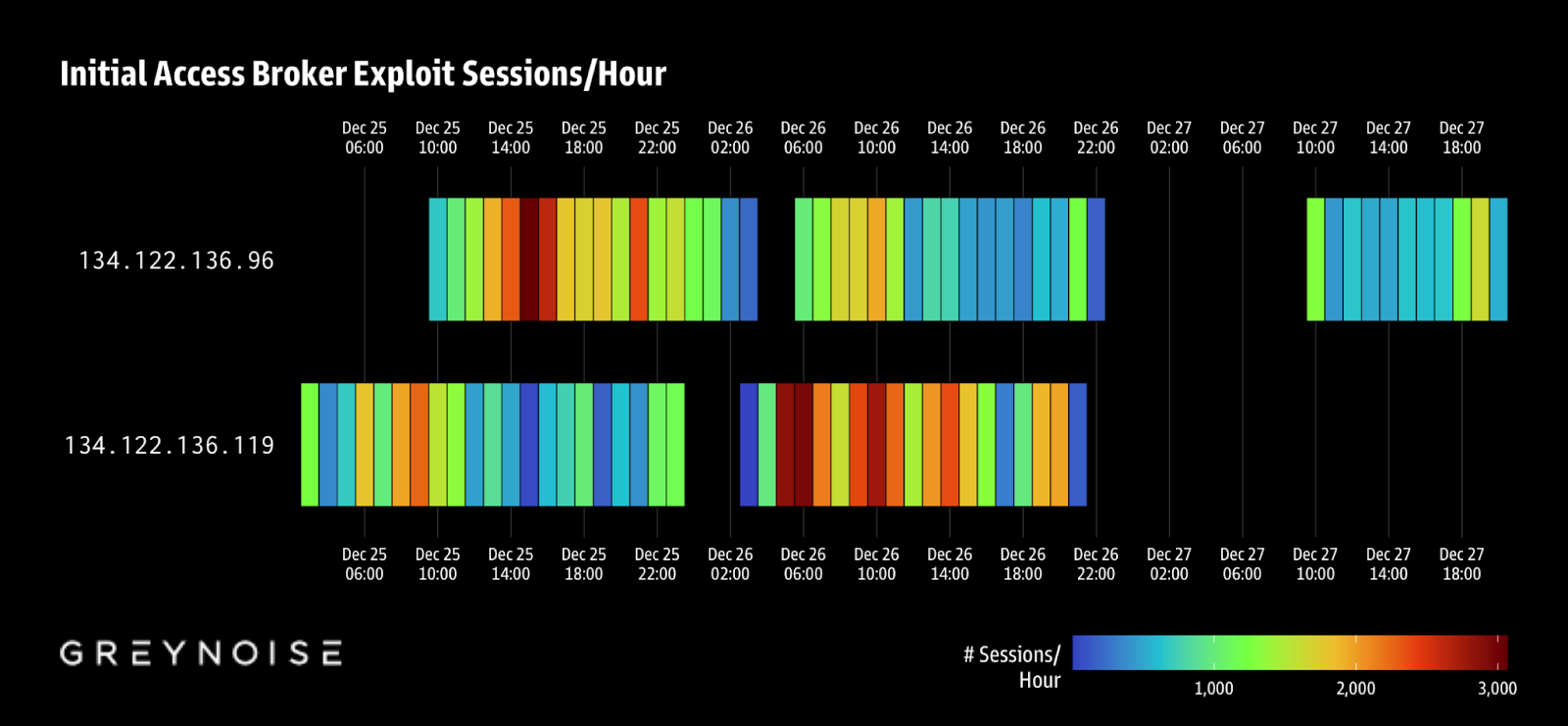
Requests came every 1–5 seconds. Each target received 11 different exploit types. The attacker used Out-of-Band Application Security Testing (OAST) domains to confirm vulnerabilities—when a system is exploited, it makes an outbound request to the attacker's callback server.
We identified over 57,000 unique OAST subdomains, all tied to ProjectDiscovery's Interactsh platform. The tooling matches what we'd expect from Nuclei, an open-source vulnerability scanner, run at industrial scale. Since the attacker used these particular domains, GreyNoise analysts were able to decode the subdomain using techniques outlined by John Jarocki/Sandia National Laboratories in a 2024 LabsCon presentation which GreyNoise has been given permission to share with this report.
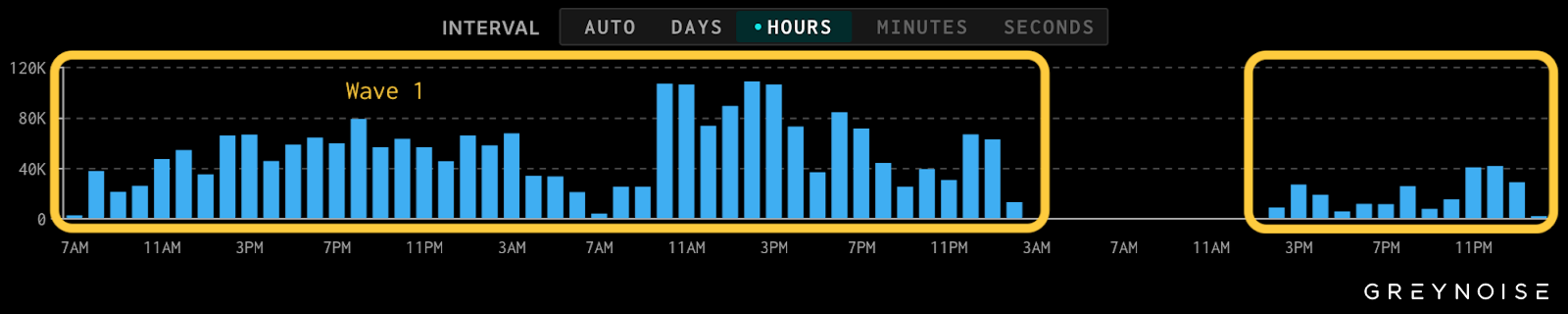
The campaign hit in two waves. Wave one used both IPs over Christmas. Wave two followed 12 hours later with a single IP, adding 13 exploit templates apparently missed in the first pass.
JA4 network fingerprints and a shared Machine ID across 98% of attempts confirm this was a single operator, not a coordinated group.
Why holiday timing matters
This wasn't random. Attackers know exactly when to hit.
Holiday periods mean skeleton security crews, delayed alert response, and reduced log review. A scanning campaign that might get flagged and blocked within hours during normal operations can run for days during a holiday weekend.
The December 25–28 window gave this operator four days of relatively unimpeded access to probe the internet. The vulnerability data harvested during that window doesn't expire when the campaign ends—it becomes a catalog for future operations.
The infrastructure question
CTG Server Limited raises flags. Despite being roughly a year old, this Hong Kong-registered hosting provider controls about 201,000 IPv4 addresses across 672 prefixes.
Prior research by Silent Push identified AS152194 as the leading ASN for phishing domains in the FUNNULL CDN infrastructure. The network also announces bogon routes—a network hygiene red flag—and multiple IP ranges appear on abuse blacklists.
This profile suggests a provider operating with minimal abuse enforcement, making it attractive for operations that need resilient infrastructure.
What to check
Review server and network logs from December 25–28 for these IPs:
134.122.136.119134.122.136.96
Examine DNS logs for queries to OAST domains:
oast.prooast.siteoast.meoast.onlineoast.funoast.live
If you find matches, assume the attacker has confirmed a vulnerability in your environment. They now have data suggesting how to get in—and that data may already be for sale.
Beyond criminal markets
We have no evidence tying this campaign to a nation-state actor. But high-quality vulnerability intelligence doesn't stay compartmentalized.
Similar reconnaissance data has historically been acquired by state-aligned groups—either through broker purchases or parallel collection efforts—to enable long-term objectives like critical infrastructure access and intelligence gathering.
The immediate concern is ransomware. The longer-term concern is that the same access paths can support espionage, sabotage, or pre-positioning for future conflict.
Expect encores
Holiday scanning campaigns aren't new, but the scale and systematization of this one stands out. Attackers will continue to exploit predictable windows when defenders are weakest.
Build that assumption into your security planning. Staff coverage during holidays matters. Detection rules for OAST callbacks matter. And if this campaign touched your infrastructure, assume someone knows exactly where your vulnerabilities are.
-----
Full campaign IoCs and the complete list of exploited vulnerability tags are published in our GitHub repository.










.png)
