Last week, the GreyNoise Observation Grid (GOG) observed something unusual: 242,666 new scanning IPs geolocating to Hong Kong appeared in seven days — nearly half of all new scanning IPs observed by GreyNoise that week. And 99.7% of them never completed a single TCP connection.
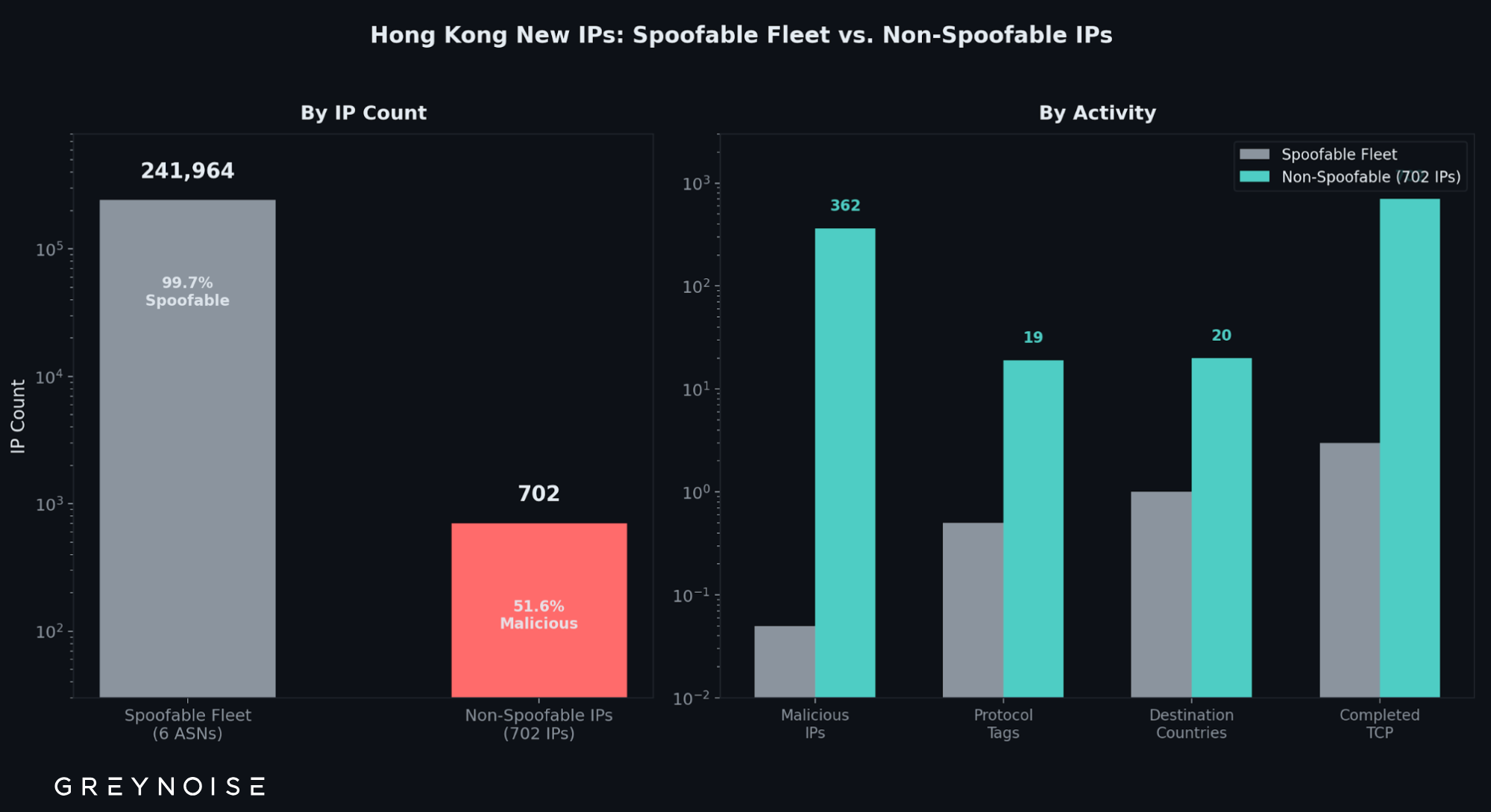
These IPs are ghosts — they appeared in GreyNoise data but never proved they were real. Because they never completed a TCP handshake, GreyNoise cannot verify that the traffic actually originated from those addresses. They carried no payloads, triggered no detection signatures, and performed no exploitation. All they left behind were a quarter-million unverified IP addresses now sitting in observation datasets.
Geographic references throughout this post describe where IPs are registered, not where the traffic necessarily originated or where operators are located.
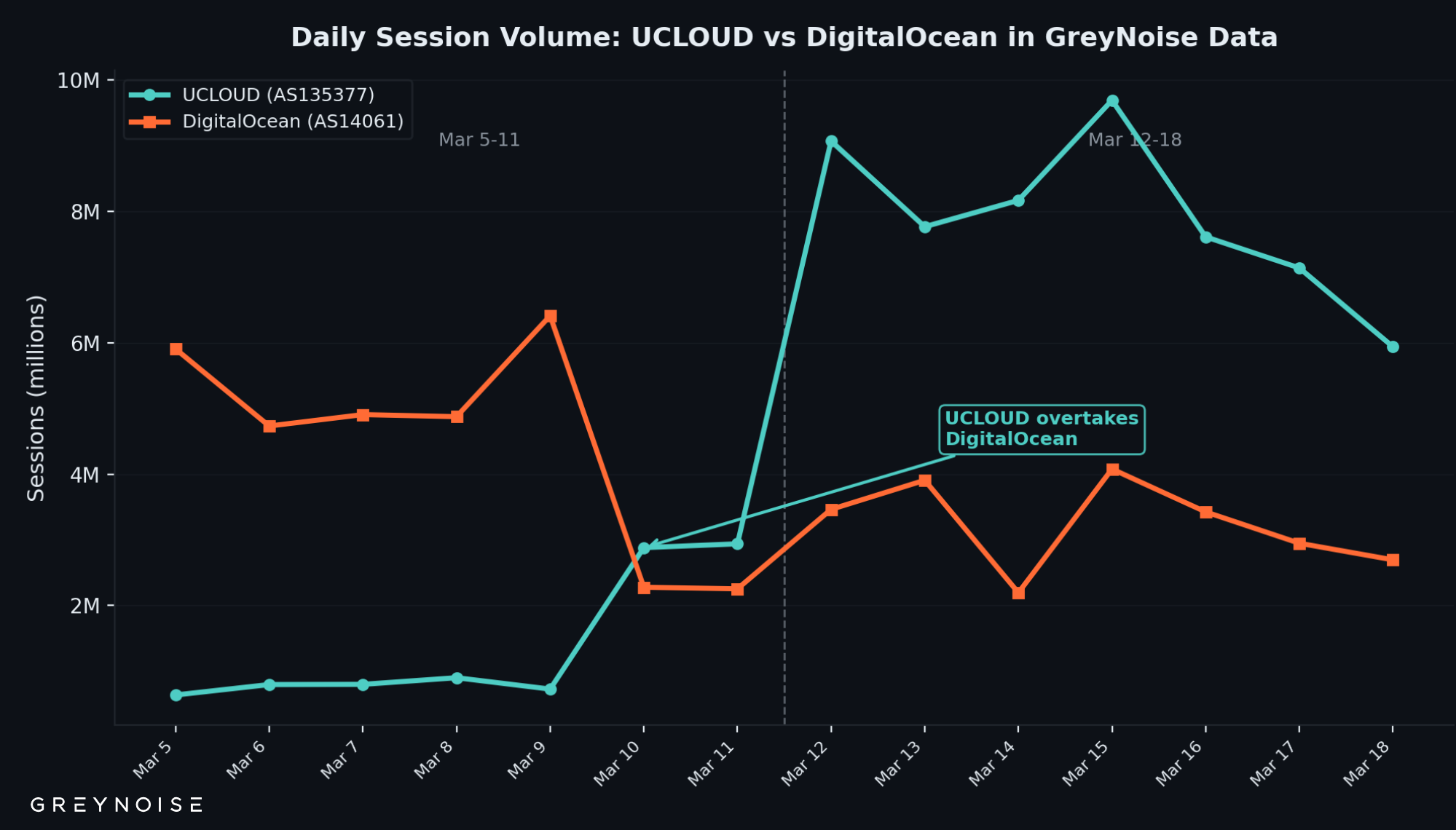
Here's why that matters: any detection system that observed this traffic and doesn't distinguish between verified and unverified source addresses just absorbed a quarter-million ghost IPs into its dataset. Meanwhile, the 702 IPs geolocating to Hong Kong that actually completed connections — the ones observed scanning MySQL, SSH, SMB, and RDP, hitting GOG sensors in 20+ countries — could easily get lost in the noise. One provider alone, UCLOUD, surged 472% in session volume to become the largest ASN by session volume in GreyNoise data, with 38% of its IPs classified malicious. That's the signal. The other 242,000 IPs are the noise.
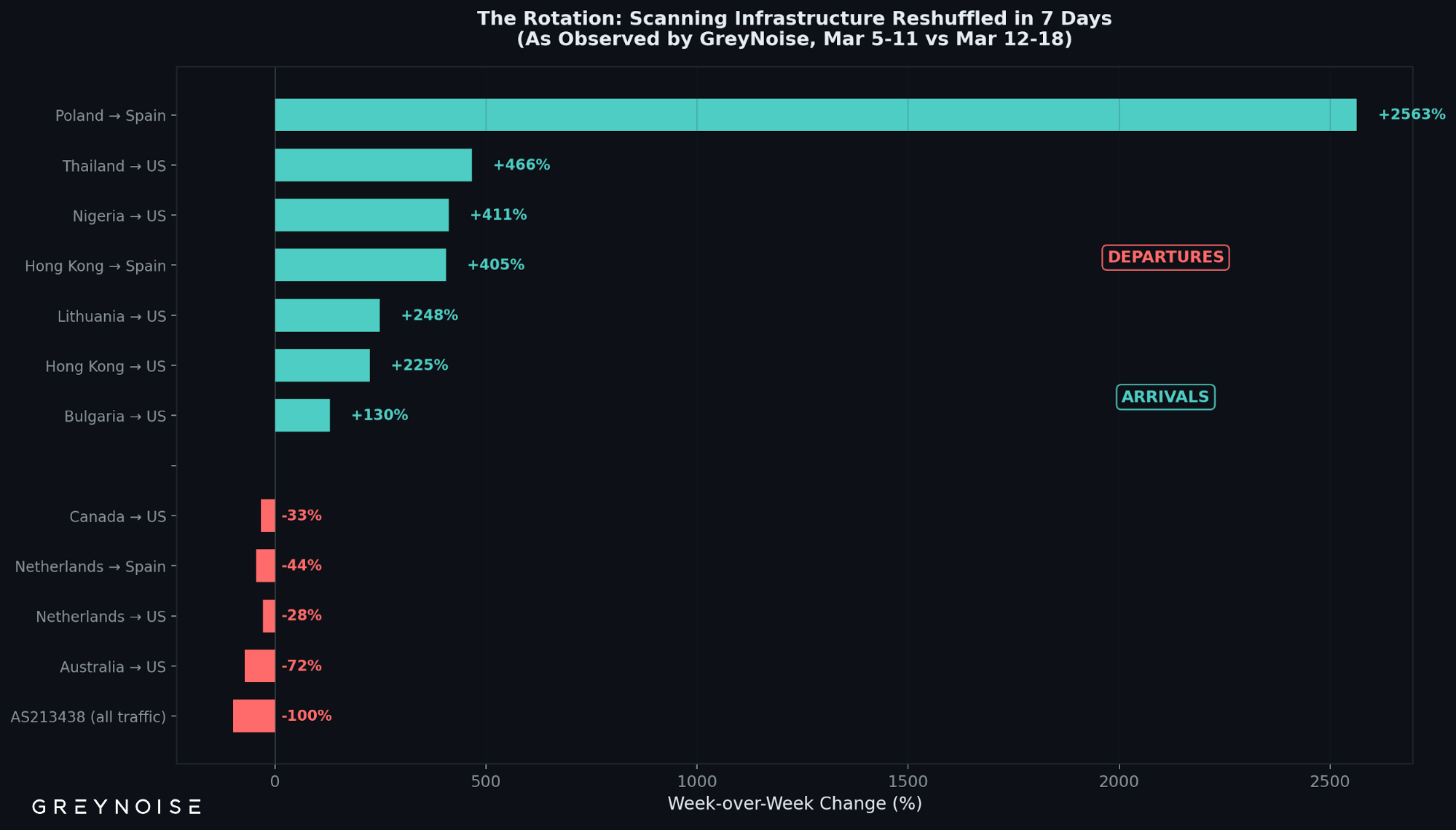
On top of that, the entire scanning landscape reshuffled last week. A top ASN disappeared overnight. Traffic from IPs geolocating to Australia dropped 72%. New infrastructure geolocating to Poland and Germany appeared. The scanning sources that dominated the prior week were not the same ones that dominated last week.
Key Findings
- 242,666 new IPs geolocating to Hong Kong — 48.9% of all new scanning IPs observed by GreyNoise last week. 99.7% never completed a TCP handshake.
- One organization, GNET INC., contributed 143,340 IPs — 28.9% of all new IPs observed by GreyNoise. Zero were classified malicious.
- Only 702 IPs geolocating to Hong Kong (0.3%) completed TCP handshakes. Of those, 362 are classified malicious.
- UCLOUD (AS135377) surged +472% in session volume, becoming the top ASN by session volume in GreyNoise data — with only 1,746 IPs but 38% classified malicious.
- The scanning landscape rotated: a top ASN from the prior week disappeared entirely, traffic from IPs geolocating to Australia dropped 72%, and new infrastructure geolocating to Poland and Germany appeared.
The Ghost Fleet
Between March 12 and 18, GreyNoise observed 242,666 new IPs geolocating to Hong Kong — nearly equal to the rest of the world combined (253,646). Six hosting providers account for 93.3%:
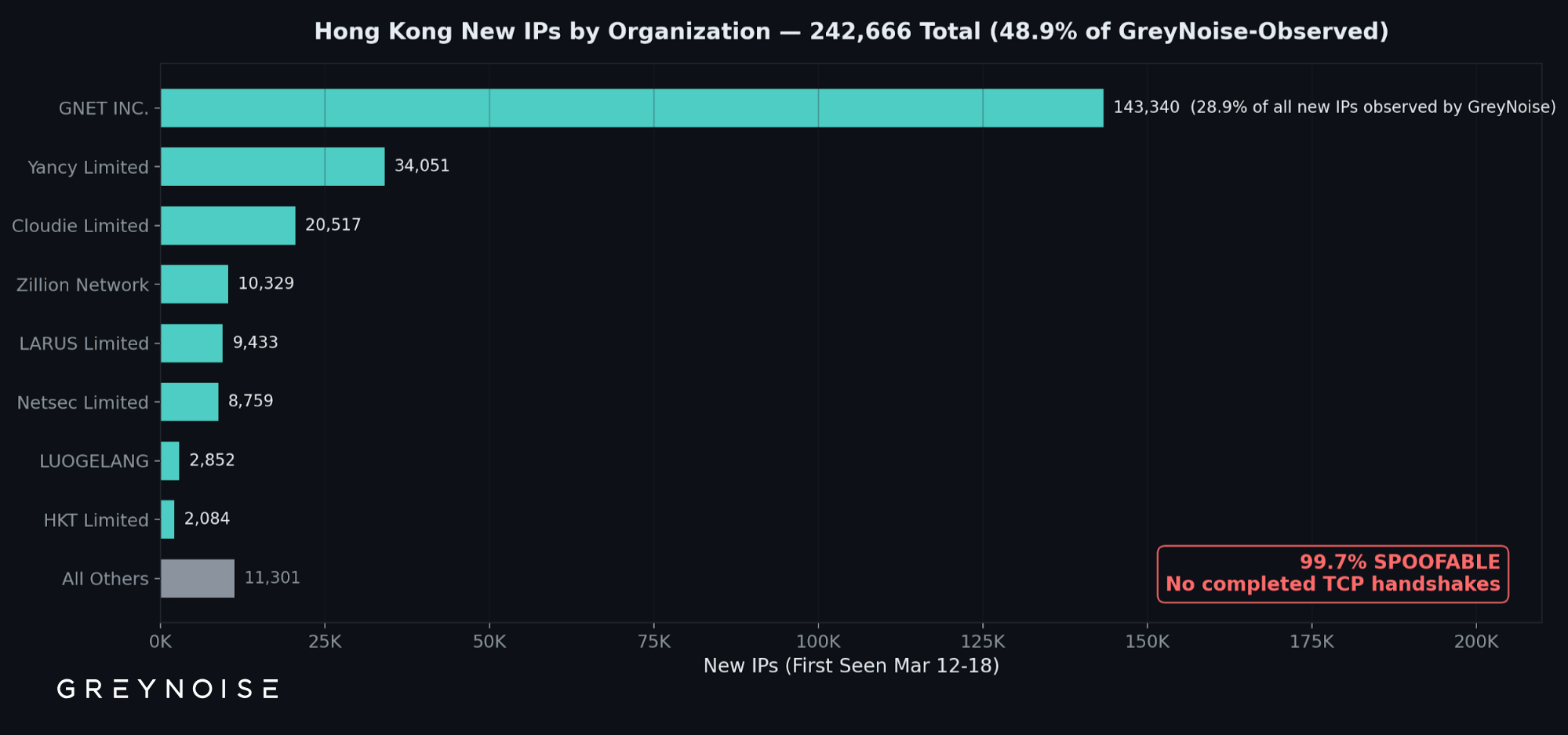
When GreyNoise labels an IP "spoofable," it means the IP was observed sending traffic but never completed a TCP three-way handshake — the source address is unverified. Of these 242,666 IPs, 241,964 are spoofable. They are classified "unknown," categorized as "hosting" infrastructure (92.3%), and carry almost no GreyNoise tags.
One Organization, 143,340 IPs, Zero Malicious
GNET INC. (AS9294) is the single largest contributor — one organization that added 28.9% of all new IPs observed by GreyNoise in a single week:
No exploitation. No brute-force activity. No web crawling. Incomplete connections only.
Names That Don't Match Registration Geography
Several ghost fleet entities are registered under names that don't align with where their IPs geolocate:
The Signal Behind the Noise: UCLOUD
The ghost fleet is the noise. The signal is UCLOUD (AS135377).
UCLOUD contributes just 1,746 IPs — 0.4% of the active IPs geolocating to Hong Kong in GreyNoise data. But it accounts for an outsized share of observed scanning and exploitation attempts:
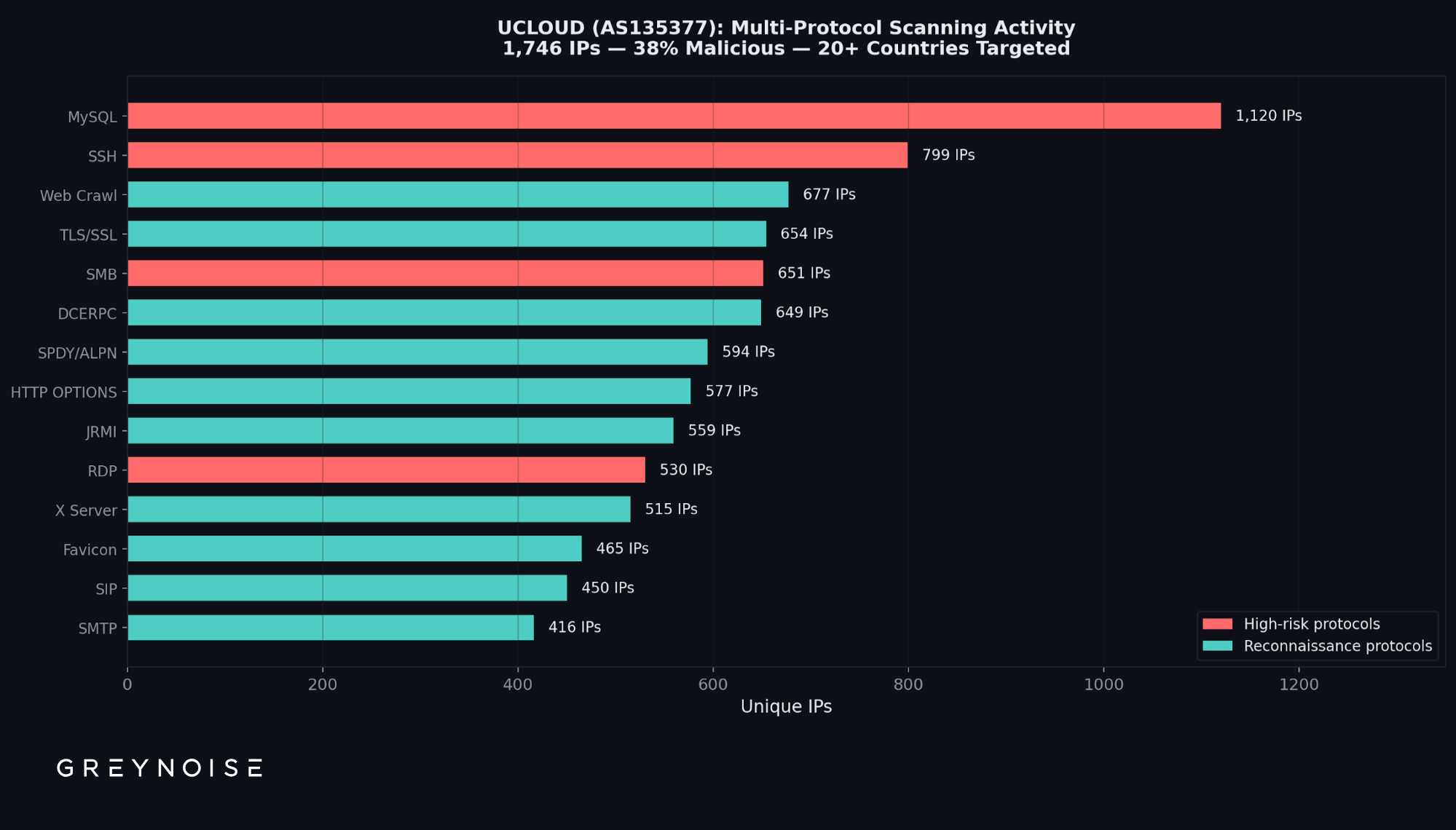
The contrast is stark. The entity generating 82x more IPs (GNET INC.) has zero classified malicious. The entity generating 82x fewer IPs (UCLOUD) has 663 — observed scanning MySQL, SSH, SMB, and RDP, with traffic reaching GOG sensors in more than 20 countries.
The Volume Surge
UCLOUD's session volume went from 9.7 million to 55.4 million in one week — displacing DigitalOcean as the top ASN by session volume in GreyNoise data:
The Rotation: Everything Shifted in Seven Days
The ghost fleet wasn't the only change. The entire scanning landscape observed by GreyNoise reshuffled. AS213438, a top ASN the prior week with 10.7 million sessions, disappeared entirely — an abrupt shutoff consistent with infrastructure being decommissioned or rotated.
What declined (source refers to IP geolocation; destination refers to GOG sensor location):
What appeared (source refers to IP geolocation; destination refers to GOG sensor location):
Under the Hood
Cross-referencing GreyNoise observations with Censys internet-wide scan data and VirusTotal reputation data reveals infrastructure patterns not visible from any single source.
Templated deployment across borders.
A cluster on infrastructure geolocating to Germany, registered to a Seychelles entity, shows configurations consistent with deployment from a single VM image. A separate Windows VPS cluster uses IPs geolocating to Bulgaria, Romania, and France across three ASNs with an identical service configuration on each node — scanning infrastructure deployed from a common template.
UCLOUD relay infrastructure.
Censys data reveals purpose-built traffic relay and tunneling software deployed across UCLOUD at a density not typical of legitimate hosting. Repeating non-standard port configurations appear identically across multiple subnets — the signature of a single VM template deployed at scale.
Low reputation detection.
The top scanning IPs are barely flagged:
What We Don't Know
GreyNoise cannot determine the purpose of the ghost fleet from GreyNoise data alone. Censys confirms these ASNs are active hosting ecosystems — the spoofable traffic uses source addresses in IP ranges distinct from the legitimate hosted infrastructure. What we can say: 242,666 IPs appeared, almost none completed connections, and the source addresses are unverified.
What Defenders Should Do
- Detection stacks that don't distinguish spoofable IPs from confirmed scanners may be affected. 242,666 unverified source addresses now exist in observation datasets. Systems that weight activity by IP count without verifying connections should be reviewed.
- Update blocklists. The sources that dominated scanning the prior week declined or disappeared, replaced by infrastructure geolocating to Hong Kong, Poland, and Germany — all within seven days.
- Monitor UCLOUD (AS135377). GreyNoise observed multi-protocol scanning activity targeting MySQL (3306), SSH (22), SMB (445), and RDP (3389).
- Track the ghost fleet ASNs for behavioral changes: AS9294, AS138415, AS55933, AS135097, AS17561, AS45753. If these IPs begin completing TCP handshakes and deploying payloads, the assessment changes.
GreyNoise is not attributing this activity to a named threat actor or state sponsor. The geographic references in this post describe where IPs are registered, not necessarily where the operators are located. Hosting infrastructure is routinely used by actors with no geographic connection to the provider's registration.






.png)
.png)













.png)




.png)















